hackers
Explore the anonymous world of criminal hackers, hacktivists and playful attention-seekers.
What is Phishing in Cyber Security? Phishing Attacks in Cyber Security Meaning Explained
Learn the definition of phishing, how these attacks work, and the best ways to stay safe online. The cyber world we live in is full of dangers, one of the biggest ones being phishing. As a cybersecurity expert, I have come across many such cases where both individuals and institutions have become a victim to wrongful actions. In this comprehensive guide, I will dive deep into the concept of phishing, exploring what it really is, the types, and the effects on our digital lives.
By ShuchiWritesabout a year ago in 01
Join the Reddy Anna Book Community with Your Unique ID. AI-Generated.
In today’s digital age, the world of books and online gaming has evolved to offer unique, convenient experiences for users. Among these innovations are the Reddy Book Id and Reddy Anna Online Book ID, which have become essential tools for accessing educational content, and the broader landscape of online gaming, which offers entertainment and skill-building opportunities. Let’s explore how these online tools are changing the way people access information, learn, and have fun.
By Allison Whiteabout a year ago in 01
Master the Future: Why Coding is Your Key to Success
I. Introduction In today's digital age, knowing how to code is super important. It's not just for tech geeks anymore—anyone can benefit from learning to code. This article will explore why coding is so valuable and how it can positively impact your life.
By creative articlesabout a year ago in 01
Apple Exposes the Truth About AI: Are We Being Lied To?
Table of Contents Introduction: Apple's Bold Claims Apple's Research on Large Language Models Why This Matters: The Impact on AI Investments Are LLMs Truly Intelligent? What Does This Mean for the Future of AI? Conclusion: Rethinking the AI Hype
By afk dgkhanabout a year ago in 01
VPN Meaning: Understanding Types of Virtual Private Networks (VPN)
Digital technologies are reshaping human life story; hence our identity could live online at a digital age. And without a doubt, for this reason, the call for combating cybercrime and cyberbullying has never been more crucial. As we navigate the perilous waters of cyber attacks, VPN is a term that we keep encountering. But what is a VPN specifically, and what is the fuss all about? In the present guide, I will delve into the real nature of Virtual Private Networks, point the way out of their different types, and share the reason why they are a must for you in your digital streaming.
By SocioSphere (PressCS)about a year ago in 01
iPhone Virus Alert! Can iPhones Get Viruses? The Truth About iOS Viruses
Describing myself as a fan of iPhones and technology, this issue usually comes up with questions about the iOS safety. This day takes me on a journey to solving a common concern that many ask: Can iPhones get viruses? In my blog, I have written this post so that the information I acquire as well as through my researches is what you get and thus may be able to have a clear understanding of iOS security and the true story of iPhone viruses.
By ShuchiWritesabout a year ago in 01
WhatsApp to Stop Working on iPhones: Key Details You Need to Know . AI-Generated.
1. Introduction What is WhatsApp? WhatsApp is one of the most popular messaging apps worldwide, offering free text messaging, voice and video calls, and media sharing. With over 2 billion active users, it has become a staple for both personal and business communications. Its cross-platform functionality, secure encryption, and simple user interface have made it a go-to app for billions.
By afk dgkhanabout a year ago in 01
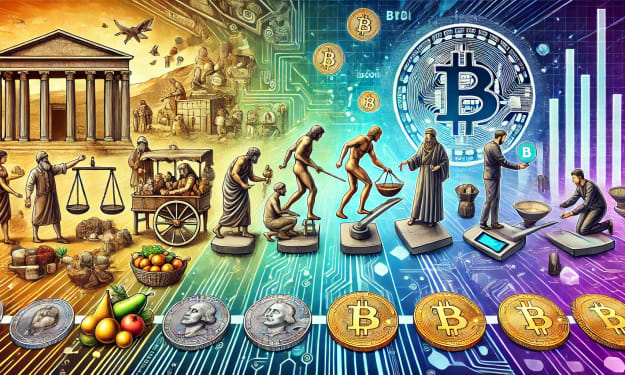
The Evolution of Currency: From Barter to Bitcoin
Paper Money: Revolutionising Trade and Commerce Money has always been a pivotal part of human civilization, from bartering to complex financial systems. Understanding this evolution helps us better appreciate the current monetary landscape and predict the future of currency. This blog follows the interesting journey of currency and its origins, key transformations, and emerging digital currencies that shape our economy today. How to Make Money with Redotpay Referral Bonus: A Step-by-Step Guide
By denizan Lawyerabout a year ago in 01
Solving Crimes Through Google Earth and Street View. AI-Generated.
In recent years, Google Earth and Google Street View have become invaluable tools for more than just navigation or exploring the world from the comfort of our homes. These technologies have aided in solving numerous crimes by providing investigators with detailed visual evidence of crime scenes, tracking suspects, and even locating missing persons. While the use of these tools for law enforcement purposes may raise concerns about privacy, the cases they’ve helped resolve highlight the significant role that digital technologies play in modern criminal investigations.
By Ganiyat Lawalabout a year ago in 01
The Dark Side of Visibility – Privacy and Surveillance in the Age of Google.. AI-Generated.
Google Street View, which launched in 2007, has become an integral part of how we navigate the world. It allows anyone with an internet connection to explore far-off places, get a feel for neighborhoods, and even peek into the streets and alleyways of cities around the globe. But beneath the surface of this seemingly innocent tool lies a darker side, particularly when it comes to privacy, data security, and surveillance. While Google’s intentions with Street View were primarily to enhance its mapping services, the unintended consequences of its data collection have raised serious ethical concerns.
By Ganiyat Lawalabout a year ago in 01
Building a Fortress: Fortifying Your Startup's Cybersecurity Culture
Imagine your startup as a bustling castle. Ideas flow freely, innovation thrives, and your team works tirelessly to build something incredible. But just like any medieval kingdom, your castle needs strong defenses to protect its treasures – in this case, your data and intellectual property. That's where cybersecurity culture comes in.
By William Walkerabout a year ago in 01